Hackers disable Swedish prosecutor's website
The website of the Swedish prosecutor's office pursuing WikiLeaks founder Julian Assange came under cyber attack on Tuesday in the latest salvo in a campaign by online supporters who have also struck PayPal and the Swiss Post Office bank.
"Our website was overloaded on Tuesday night and our hosting company then decided to shut it down. We don't know the cause of the overload, but are now looking into it," Karin Rosander, a spokesperson for the Swedish Prosecution Authority (Åklagarmyndigheten) told the TT news agency.
She added that she had not yet received confirmation that the site outage was caused by a hacker attack.
PandaLabs, the malware detection laboratory for computer security firm Panda Security, said the prosecutor's website, aklagare.se, was brought down by members of the loose "cyber hacktivist" group called "Anonymous."
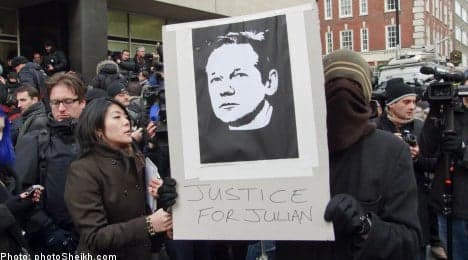
The attack on the Swedish prosecutor's website came as Assange, whose release of secret US diplomatic cables has sparked an international furor, was refused bail by a British judge over allegations of sex crimes in Sweden.
As of 6.30am Wednesday morning, the prosecutor's website remained inaccessible, but by 8.30am it was up and running again.
Sean-Paul Correll, a threat researcher at PandaLabs, said Anonymous had dubbed the attacks on the websites of the Swedish prosecutor's office, PayPal and the Swiss Post Office bank as "Operation Avenge Assange."
He said they were part of a battle being waged online between supporters and opponents of WikiLeaks, whose website has come under repeated cyber attack itself and has seen US companies gradually withdrawing their support.
"We have two sides of this attack spectrum," the PandaLabs researcher told AFP in a telephone interview.
"We have the Anonymous guys on one side fighting for freedom of information and freedom of press," Correll said.
"And we have other people who consider themselves patriots who are trying to defend the greater interests of the United States."
Asked if he believed there was US government involvement behind the cyber attacks on the WikiLeaks website, Correll said "it's tough to say."
"It would just be speculation because no one has come forward to say that there is some type of involvement," he said.
He noted that an early attack on the WikiLeaks website had been claimed by a known hacker who calls himself the "Jester."
"The Jester doesn't necessarily have to be one person," he said.
"It could be a group of people, of patriots."
WikiLeaks has been under cyber attack since Assange began releasing the first US documents last week, forcing it to repeatedly change addresses and Web hosts.
Amazon dropped WikiLeaks from its servers last week and PayPal blocked financial transfers to the site while the Swiss Post Office bank on Monday closed accounts held by Assange, the Australian-born WikiLeaks founder.
PayPal's official blog, ThePayPalBlog.com, came under distributed denial of service, or DDoS, attack on Saturday and was down for at least eight hours, PandaLab's Correll said.
He said that as of 6:00 pm (2300 GMT) on Tuesday, the Swiss Post Office bank site had been down for more than 20 hours.
"Someone actually posted on Twitter and asked the attackers to stop their attacks so they can conduct their banking," Carroll said.
In a classic DDoS attack, a "botnet" of zombie computers, machines infected with viruses, are commanded to simultaneously visit a website, overwhelming its servers, slowing service or knocking it offline completely.
Correll said the Swedish prosecutor's website was attacked by over 500 computers at the direction of Anonymous. "It literally went down the second they announced the target," he said.
The PandaLabs researcher said Anonymous included anti-copyright activists who took part in "Operation Payback," which began in September and involved cyber attacks on the websites of the Motion Picture Association of America (MPAA) and the Recording Industry Association of America (RIAA).
"This past weekend they decided they were going to fight against anybody anti-WikiLeaks," said Correll, adding that he has been following Anonymous "from Day One."
"Anonymous doesn't have a central authority, there's no hierarchical structure," he said.
"People describe it as having a kind of hive mind mentality."
"They use social networks to recruit members and chat infrastructure," he said, adding that "right now there's over 1,000 people in their chat room participating in their attacks."
"These guys are very resourceful," Correll said, adding that he expects their retaliatory activities to go beyond just DDoS attacks.
"I expect a laundry list of targets," he said. "They'll research security vulnerabilities on a website. They've defaced websites in the past so I expect to see all sorts of things coming in the future."
Comments
See Also
"Our website was overloaded on Tuesday night and our hosting company then decided to shut it down. We don't know the cause of the overload, but are now looking into it," Karin Rosander, a spokesperson for the Swedish Prosecution Authority (Åklagarmyndigheten) told the TT news agency.
She added that she had not yet received confirmation that the site outage was caused by a hacker attack.
PandaLabs, the malware detection laboratory for computer security firm Panda Security, said the prosecutor's website, aklagare.se, was brought down by members of the loose "cyber hacktivist" group called "Anonymous."
The attack on the Swedish prosecutor's website came as Assange, whose release of secret US diplomatic cables has sparked an international furor, was refused bail by a British judge over allegations of sex crimes in Sweden.
As of 6.30am Wednesday morning, the prosecutor's website remained inaccessible, but by 8.30am it was up and running again.
Sean-Paul Correll, a threat researcher at PandaLabs, said Anonymous had dubbed the attacks on the websites of the Swedish prosecutor's office, PayPal and the Swiss Post Office bank as "Operation Avenge Assange."
He said they were part of a battle being waged online between supporters and opponents of WikiLeaks, whose website has come under repeated cyber attack itself and has seen US companies gradually withdrawing their support.
"We have two sides of this attack spectrum," the PandaLabs researcher told AFP in a telephone interview.
"We have the Anonymous guys on one side fighting for freedom of information and freedom of press," Correll said.
"And we have other people who consider themselves patriots who are trying to defend the greater interests of the United States."
Asked if he believed there was US government involvement behind the cyber attacks on the WikiLeaks website, Correll said "it's tough to say."
"It would just be speculation because no one has come forward to say that there is some type of involvement," he said.
He noted that an early attack on the WikiLeaks website had been claimed by a known hacker who calls himself the "Jester."
"The Jester doesn't necessarily have to be one person," he said.
"It could be a group of people, of patriots."
WikiLeaks has been under cyber attack since Assange began releasing the first US documents last week, forcing it to repeatedly change addresses and Web hosts.
Amazon dropped WikiLeaks from its servers last week and PayPal blocked financial transfers to the site while the Swiss Post Office bank on Monday closed accounts held by Assange, the Australian-born WikiLeaks founder.
PayPal's official blog, ThePayPalBlog.com, came under distributed denial of service, or DDoS, attack on Saturday and was down for at least eight hours, PandaLab's Correll said.
He said that as of 6:00 pm (2300 GMT) on Tuesday, the Swiss Post Office bank site had been down for more than 20 hours.
"Someone actually posted on Twitter and asked the attackers to stop their attacks so they can conduct their banking," Carroll said.
In a classic DDoS attack, a "botnet" of zombie computers, machines infected with viruses, are commanded to simultaneously visit a website, overwhelming its servers, slowing service or knocking it offline completely.
Correll said the Swedish prosecutor's website was attacked by over 500 computers at the direction of Anonymous. "It literally went down the second they announced the target," he said.
The PandaLabs researcher said Anonymous included anti-copyright activists who took part in "Operation Payback," which began in September and involved cyber attacks on the websites of the Motion Picture Association of America (MPAA) and the Recording Industry Association of America (RIAA).
"This past weekend they decided they were going to fight against anybody anti-WikiLeaks," said Correll, adding that he has been following Anonymous "from Day One."
"Anonymous doesn't have a central authority, there's no hierarchical structure," he said.
"People describe it as having a kind of hive mind mentality."
"They use social networks to recruit members and chat infrastructure," he said, adding that "right now there's over 1,000 people in their chat room participating in their attacks."
"These guys are very resourceful," Correll said, adding that he expects their retaliatory activities to go beyond just DDoS attacks.
"I expect a laundry list of targets," he said. "They'll research security vulnerabilities on a website. They've defaced websites in the past so I expect to see all sorts of things coming in the future."
Join the conversation in our comments section below. Share your own views and experience and if you have a question or suggestion for our journalists then email us at [email protected].
Please keep comments civil, constructive and on topic – and make sure to read our terms of use before getting involved.
Please log in here to leave a comment.